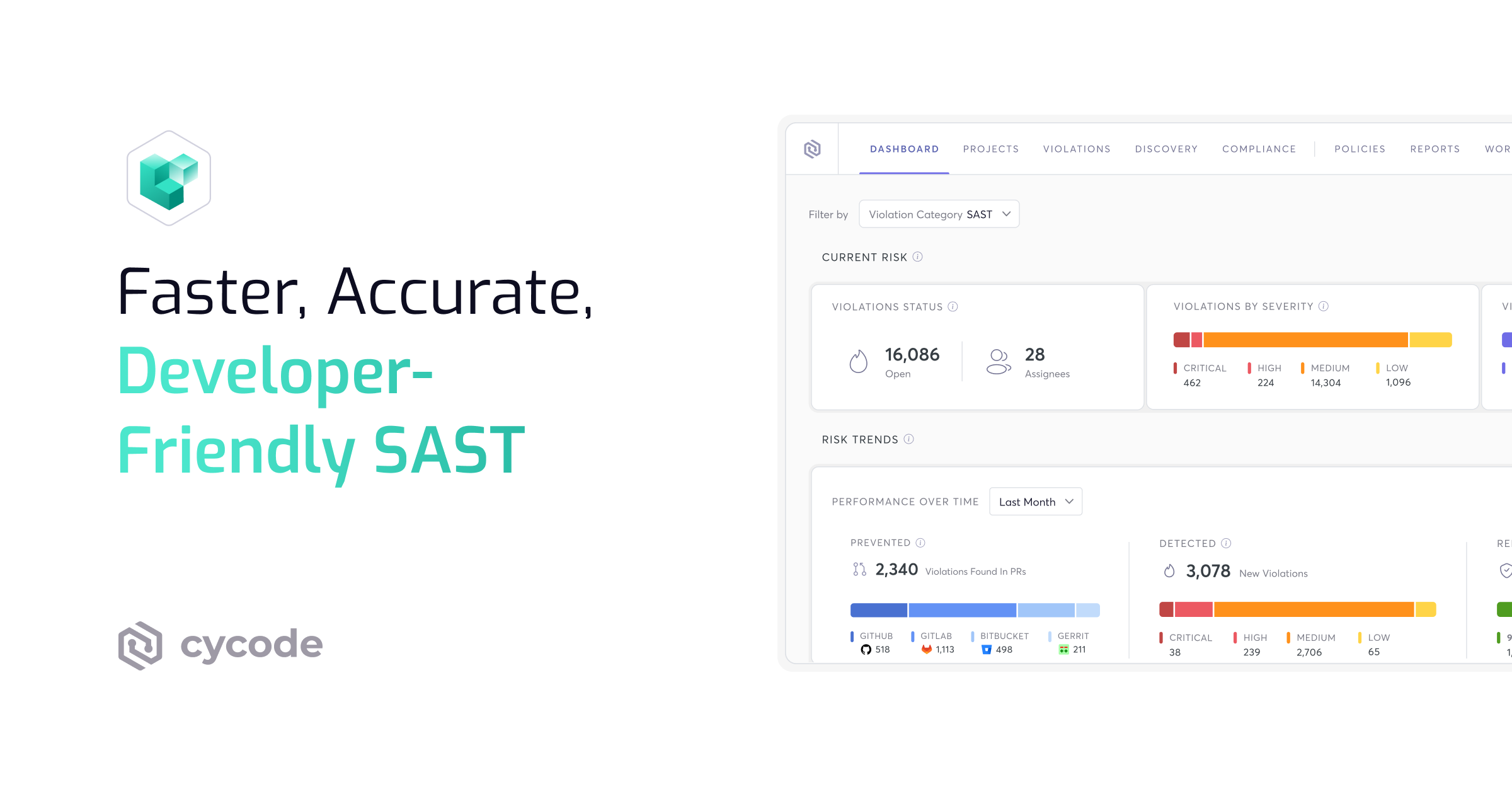
Faster, Accurate,
Developer-Friendly SAST Scanner
Enhance the security of your code from the get-go with static application security testing (SAST) designed by developers, for developers.
{ Scanning }
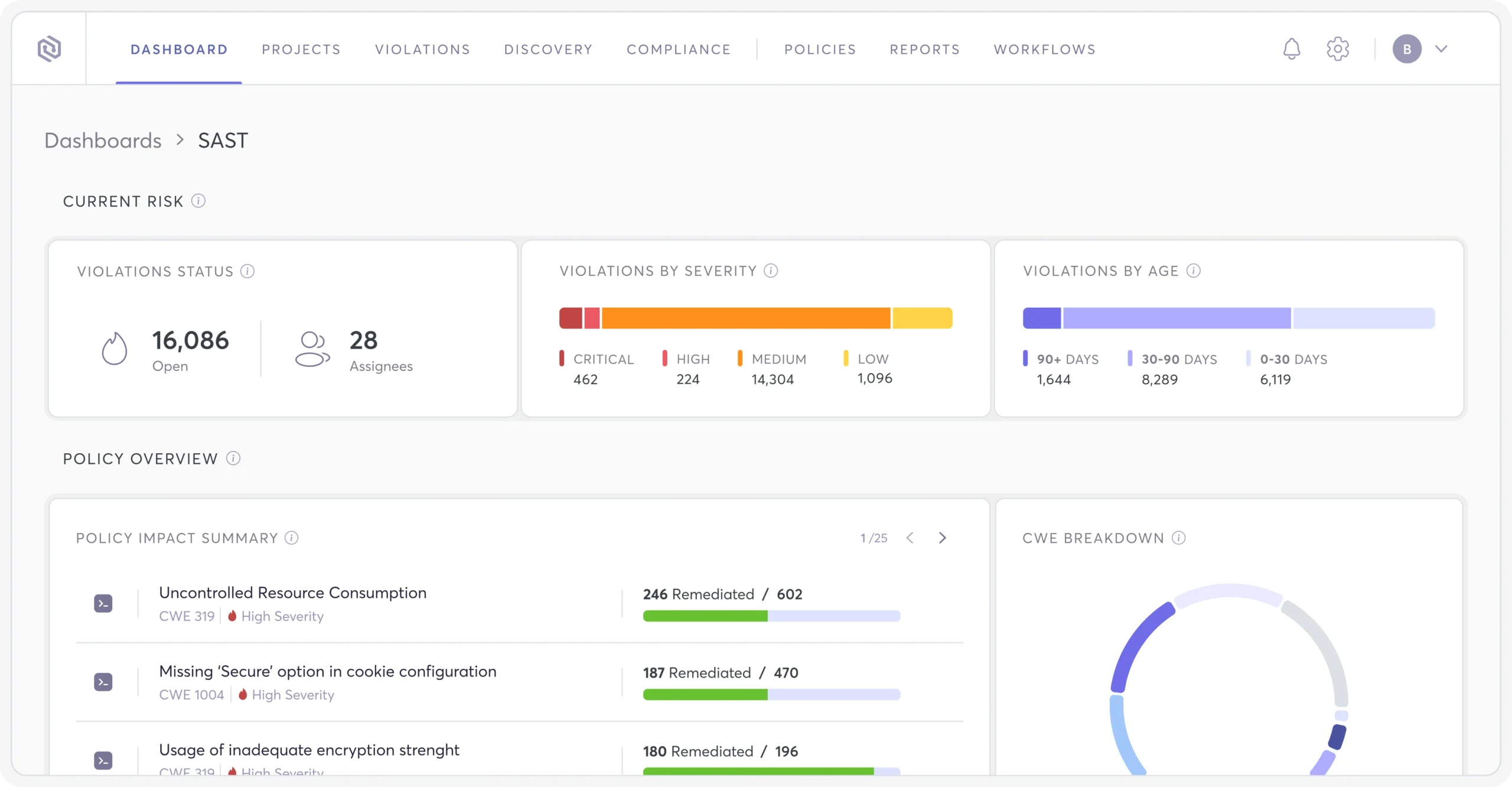
Continuous SAST Scanning Built
for DevOps Velocity
Keep delivering software fast with 31% faster SAST scanning that enables you to find and fix vulnerabilities in code without
disrupting the speed of development.
Continuously scan every code change
OWASP top 10 vulnerability detection
Customizable detection logic
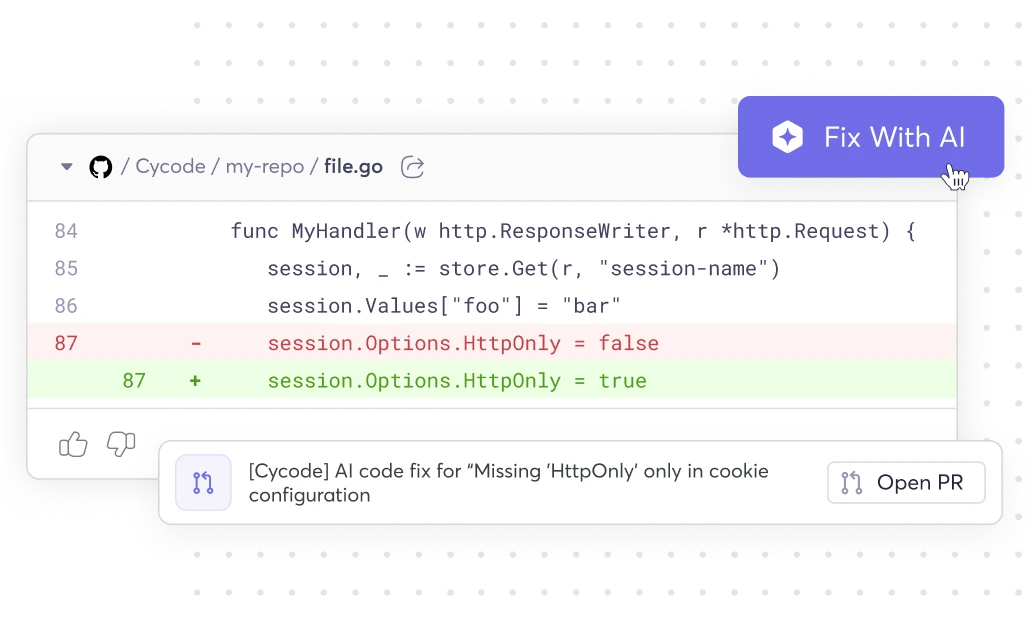
{ Remediation }
AI-Driven Context
for Faster Remediation
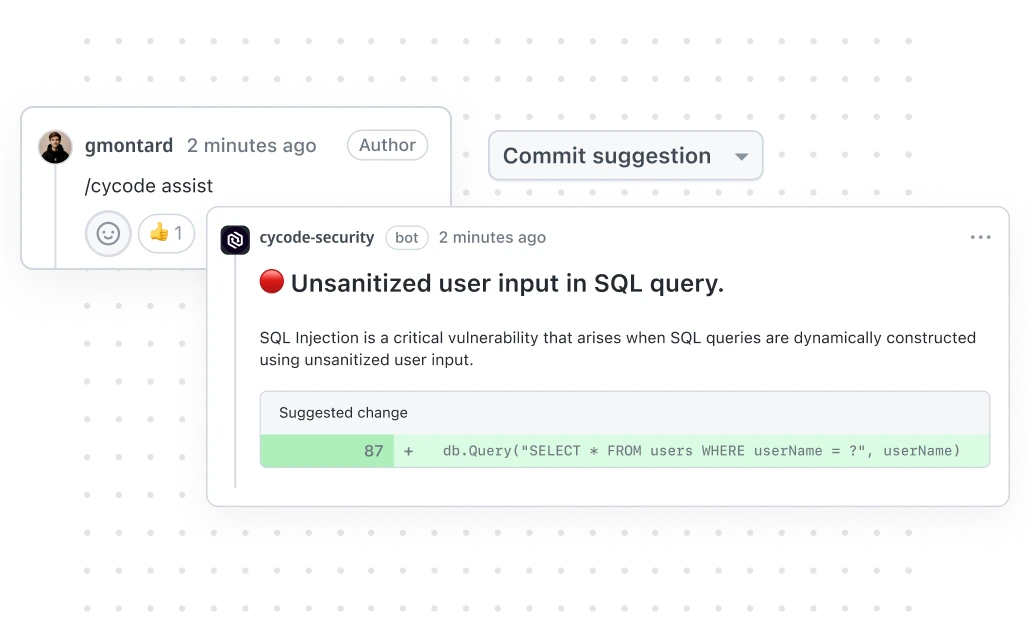
Find customized explanations ready and waiting for every security issue. Leverage Cycode’s Risk Intelligence Graph (RIG) for AI-enabled code to cloud traceability across the SDLC, providing insights from development to production. No more wasting developers’ time on non-critical findings.
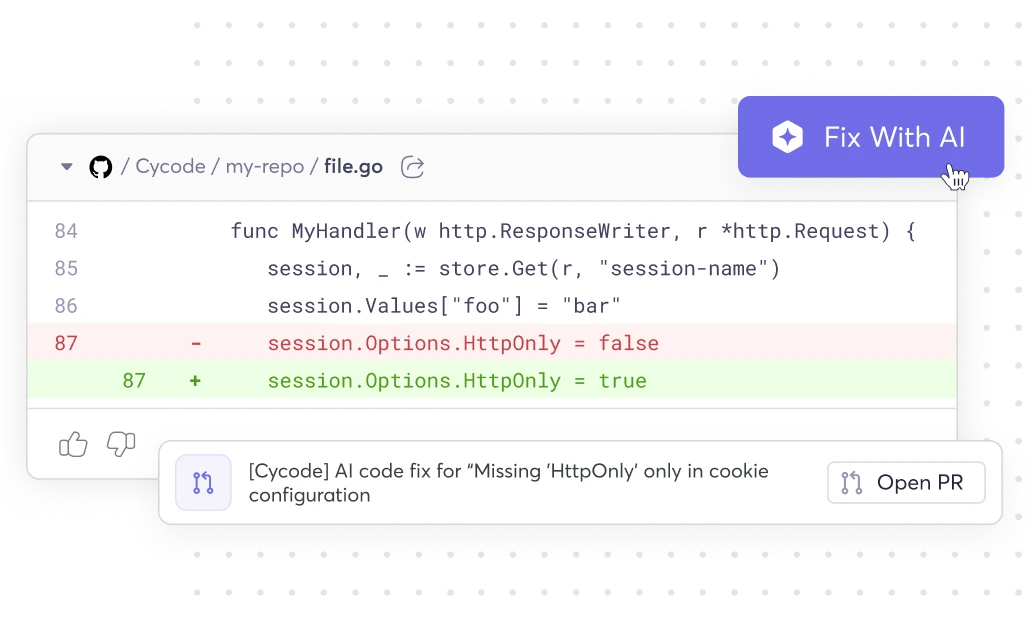
AI-suggested code fixes
AI-powered context via the RIG
Enhanced precision for the most accurate results
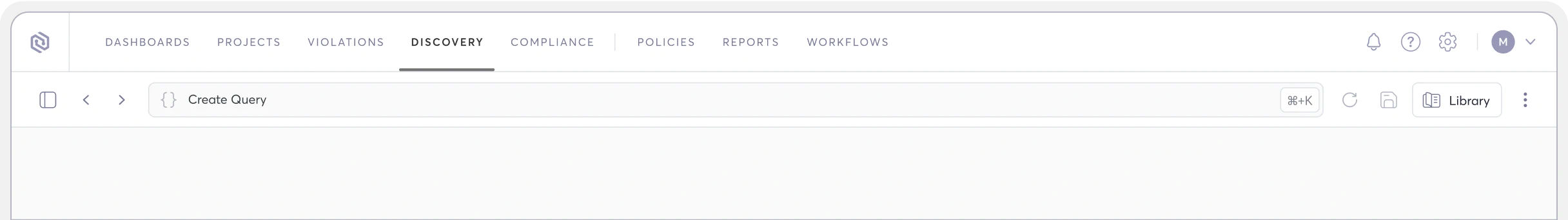
{ Experience }
Unparalleled Developer Experience
Developer-friendly static code analysis so you can enforce security standards across all your apps from a single platform.
Built-in rules for each language
Custom rules
Live terminal execution
Pull request scanning
{ Coverage }
Complete Stack Support
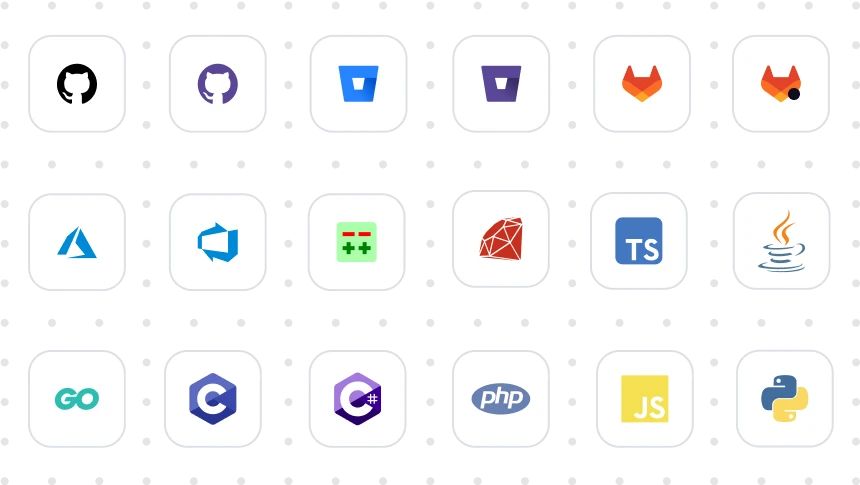
Cycode SAST supports a wide range of programming languages and
SCMs, and our coverage is constantly expanding.
Language support for Java, C#, JavaScript, PHP, Python, Ruby, Go, and many more.
SCM support for GitHub, GitLab, BitBucket, Azure DevOps, Gerrit, and more.
{ Protection }
Enterprise SAST Analysis Designed to Scale
Cycode’s SAST solution goes beyond vulnerability detection. It delivers real business value at scale. By combining enterprise-grade accuracy with developer-friendly workflows, organizations can:
Accelerate remediation with prioritized, high-fidelity results that cut through noise
Reduce risk exposure by identifying vulnerabilities early in the SDLC
Lower operational costs by consolidating tools and streamlining workflows
Improve developer productivity with context-rich insights directly in existing pipelines
Reliable SAST Scanning Tools Built to Scale with Your Enterprise
Our enterprise-grade SAST scanning solution is engineered for speed and precision. It delivers comprehensive security results directly within your CI/CD pipeline, so you can find and fix vulnerabilities that matter.
Visibility into Proprietary Code Risks
A modern SAST solution provides deep, contextual visibility into your proprietary code. By analyzing your entire codebase, our platform uncovers security vulnerabilities and helps you understand the full scope of your application's risks, ensuring nothing is missed.
Prioritization That Cuts False Positives
With our platform, you can say goodbye to alert fatigue. Our risk-based approach to SAST code scanning prioritizes vulnerabilities with a dramatically low false-positive rate, ensuring your teams focus only on the issues that pose a real threat to your business and can be remediated quickly.
Code Security Scanning Tools That Enhance Your SDLC
The right tools should fit seamlessly into your existing workflows. Our SAST solution integrates directly with your CI/CD pipelines, providing developers with immediate, actionable feedback in their native environments, helping them fix issues early and move with speed.
SAST Scans that Secure Code without Slowing Delivery
Security reviews shouldn't be the reason your release is late. Traditional SAST scanning forces teams to choose between thoroughness and speed, run a full scan and wait, or skip it and ship blind. Modern AI-powered SAST removes that tradeoff entirely by embedding scans directly into your development workflow, catching issues in real time without creating bottlenecks in your pipeline.
{ Developer-First Execution }
Reduce Friction in the Dev Workflow
Modern SAST runs continuously in the background of your CI/CD pipeline, surfacing findings as developers write and commit code, not hours or days later in a separate review cycle.
Scan results appear inline in pull requests and IDE environments, so developers see issues where they already work.
Automated triage filters out noise and surfaces only the findings that are reachable and exploitable.
Remediation guidance ships with every finding, including AI-suggested fixes that developers can apply in one click.
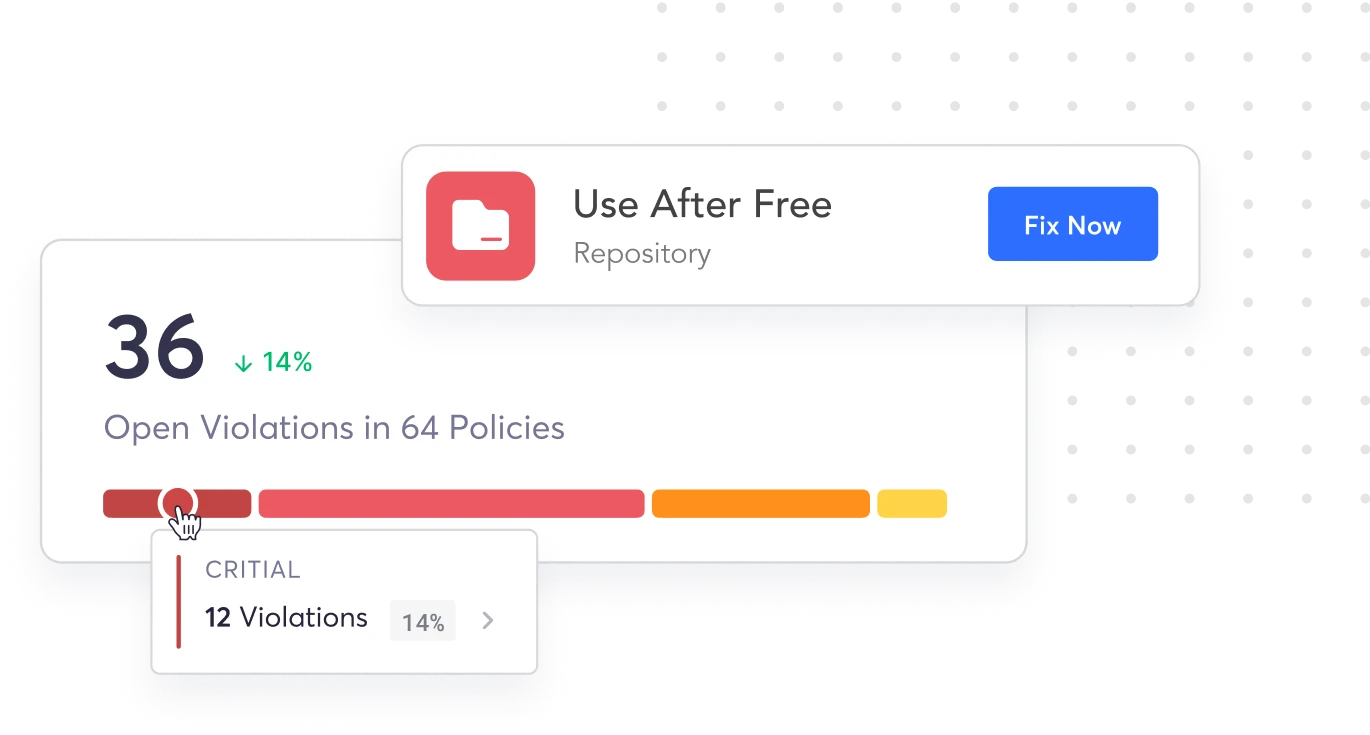
{ Risk-Based Precision }
Prioritize What Actually Matters
Most SAST tools bury real risks under hundreds of low-severity alerts. That kind of noise teaches developers to ignore findings altogether. A risk-based approach flips this by scoring each vulnerability against exploitability, business context, and exposure, so your team spends time on threats that could actually cause damage.
Contextual risk scoring weighs factors like reachability, data sensitivity, and whether the vulnerable path is exposed to external input.
Correlated findings across SAST, SCA, and secrets detection reduce duplicate alerts and give a single prioritized view.
Trend reporting tracks your risk posture over time, giving security leaders clear evidence of progress without chasing vanity metrics.
Frequently Asked Questions About SAST
What is SAST tool?
Cycode’s SAST scanner takes this a step further by delivering enterprise-grade accuracy, seamless integration, and risk-based prioritization. Designed for scale, it empowers organizations to fix what matters most by providing context-rich insights, streamlined remediation, and a developer-friendly experience across the entire software development lifecycle (SDLC).
Where Does SAST Scanning Fit in CI/CD Workflows?
The key is making sure scan results don't block deployments unnecessarily. A well-configured SAST integration uses severity thresholds and risk-based policies to determine what should fail a build versus what gets flagged for review. That way, critical vulnerabilities stop bad code from shipping, while lower-risk findings get tracked without grinding your pipeline to a halt. For teams running complex CI/CD pipelines, SAST is one layer in a broader security strategy, working alongside SCA, secrets detection, and IaC scanning to cover the full attack surface from code to cloud.
Why Is SAST Analysis Critical in the SDLC?
With Cycode’s SAST, organizations also see faster release cycles, fewer false positives, and greater alignment between security and development teams, turning secure coding into a business advantage rather than a bottleneck.
How Do Enterprise Solutions Compare to Open Source SAST Tools?
Enterprise scanners, including AI-native application security platforms like Cycode, come with dedicated support, pre-built integrations for major CI/CD systems, and consistent update cycles. You trade cost for lower maintenance overhead and more predictable results. Open-source SAST tools offer flexibility and zero licensing cost, but they require more hands-on setup, ongoing maintenance, and custom integration work. Update frequency and detection quality can also vary significantly depending on the project's contributor activity.
|
Offering
|
Enterprise SAST
|
Open-Source SAST
|
|---|---|---|
|
Support
|
Extensive
|
Limited
|
|
Integration
|
Robust
|
Requires Effort
|
|
Cost
|
High
|
Low
|
|
Update frequency
|
Regular
|
Varies
|
|
Quality
|
Consistent
|
Inconsistent
|
It's also worth distinguishing between traditional and modern SAST tools. Traditional scanners have been around for over 25 years, and they're known for slow scan times and high false-positive rates. These issues make developers reluctant to run scans early in the process, which defeats the purpose.
Modern SAST scanners are built for speed and precision. They produce fewer false positives, integrate natively into developer workflows, and support continuous delivery. Most also include AI-powered fix suggestions, so remediation doesn't require a security expert to interpret every finding.
|
Feature
|
Traditional SAST
|
Modern SAST
|
|---|---|---|
|
Scanning Speed
|
Slow
|
Fast
|
|
Integration
|
Robust
|
Requires Effort
|
|
False Positive Rates
|
High
|
Low
|
|
Developer Experience
|
Poor
|
Enhanced
|
|
Automation
|
Minimal
|
Robust
|
Beyond point solutions, an Application Security Posture Management (ASPM) platform covers the entire SDLC, including all components, tools, libraries, languages, CI/CD pipelines, and cloud infrastructure. A complete ASPM solution bundles its own proprietary scanners (SAST, SCA, IaC, and more) into a single platform, giving teams a unified view of security across the development lifecycle. It also lets you plug in third-party tools you already use, so you get full coverage without ripping out your existing stack..
What Tools Can Be Used for SAST Security?
On the other hand, open-source SAST scanning tools provide flexibility and cost savings but require more effort to set up and maintain. There’s also the risk of delayed updates and inconsistent quality, which can leave applications vulnerable.
| Offering | Enterprise SAST | Open-Source SAST |
|---|---|---|
| Support | Extensive | Limited |
| Integration | Robust | Requires Effort |
| Cost | High | Low |
| Update frequency | Regular | Varies |
| Quality | Consistent | Inconsistent |
In contrast, a modern SAST scanner offers faster speeds and more precise findings, enhances the developer experience, and supports continuous code delivery. It also tends to incorporate AI-powered code resolution for automated fix suggestions, streamlining the remediation process.
| Feature | Traditional SAST | Modern SAST |
|---|---|---|
| Scanning Speed | Slow | Fast |
| Integration | Robust | Requires Effort |
| False Positive Rates | High | Low |
| Developer Experience | Poor | Enhanced |
| Automation | Minimal | Robust |
A complete ASPM platform offers its own proprietary scanning tools, including SAST, IaC, SCA, and more, into one solution, providing a unified approach to securing applications that addresses vulnerabilities across the development lifecycle and all components. It also allows you to integrate any of your third-party tools. This holistic approach ensures robust measures are in place at every stage, enhancing overall posture and efficiency.
How Does Static Application Security Testing Work?
Where Does SAST Scanning Fit in CI/CD Workflows?
SAST vs DAST vs SCA: What’s the Difference?
The three approaches catch different types of problems at different stages. SAST finds issues like injection flaws, hardcoded credentials, and insecure logic in your own code, typically during development. DAST uncovers runtime problems like authentication weaknesses, misconfigured headers, and server-side errors, usually in a staging or production environment. SCA identifies known CVEs in your dependencies and flags licensing conflicts, at build time or in your artifact registry.
None of them covers everything on its own. Most security teams use all three together to get meaningful coverage across both custom code and third-party components.
|
Key Differences
|
SAST
|
DAST
|
SCA
|
|---|---|---|---|
|
What It Analyzes
|
Proprietary source code, bytecode, or binaries.
|
Running application (black-box testing).
|
Open-source libraries and third-party dependencies.
|
|
When It Runs in the SDLC
|
During development (commit, PR, CI build).
|
Post-deployment (staging or production).
|
At build time or in artifact registries.
|
|
Types of Risks Identified
|
Code-level flaws: injection, XSS, hardcoded secrets, insecure logic.
|
Runtime issues: auth bypasses, misconfigurations, server errors.
|
Known CVEs in dependencies, license violations, outdated components.
|
Together, SAST and SCA cover the codebase end to end: your code plus everything it pulls in. Adding DAST closes the gap by testing how the application actually behaves once it's running. For teams that want all three under one roof, an ASPM platform like Cycode consolidates scanning, prioritization, and remediation into a single workflow.
What Problems Do Cycode’s Static Application Security Testing Tools Solve?
It also helps address the challenge of maintaining security across large, complex codebases by continuously scanning for issues and providing actionable feedback. By integrating into CI/CD pipelines, SAST enables enterprises to catch vulnerabilities early, reducing friction between security and development teams while accelerating software delivery.
What Kind of Vulnerabilities Can a SAST Scan Find?
- SQL injection
- Cross-site scripting (XSS)
- Buffer overflows
- Insecure authentication mechanisms
How Can Cycode’s SAST Security Tools Support Compliance Requirements?
Our SAST scanner provides the visibility and evidence needed to demonstrate adherence to frameworks such as NIST Secure Software Development Framework (SSDF), FedRAMP, and other regulatory mandates. With automated reporting and continuous monitoring, Cycode simplifies audits, accelerates attestations, and ensures that compliance isn’t just a checkbox, but a natural outcome of your development process.
What Should Enterprises Look for in Modern SAST Solutions?
- High-fidelity results with risk-based prioritization to cut false positives
- Scalability to handle large, complex codebases and multi-language environments
- Proprietary scanners that deliver enterprise-grade accuracy beyond open-source engines
- Seamless integrations across CI/CD pipelines, IDEs, and existing security tools
- Developer-first workflows with contextual insights and automated remediation support
- Comprehensive reporting to meet compliance and executive visibility needs

 Solution Brief
Solution Brief