Secrets Detection and Scanning
by Cycode
Continuously scan, detect and remediate every hidden secret across your
SDLC and developer productivity tools
{ visibility }
Scan Code & Beyond to
Find All Your Exposed Secrets
Secrets hide in a lot of places that aren’t just source code. Make sure you find and fix them all.
Get a DemoAI powered secrets detection
Extend secrets detection across ticketing, documentation, and messaging tools
Identify secrets across the SDLC
Pre-defined rules to detect secrets for both known and proprietary services
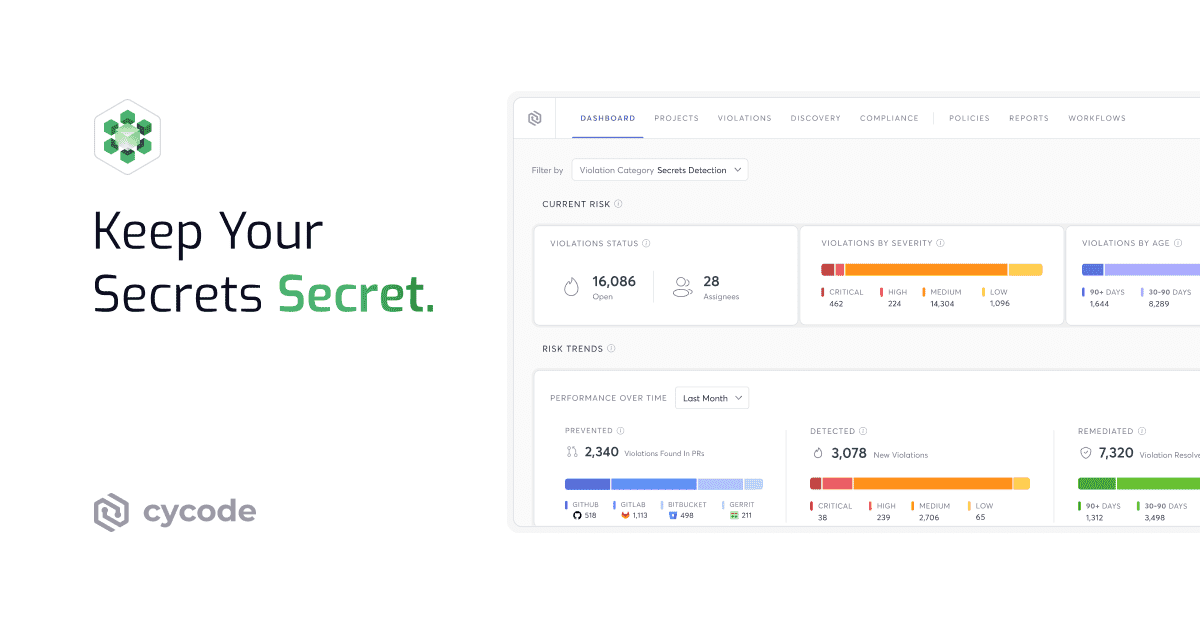
{ Prioritization }
Not All Secrets
Are Created Equal
Prioritize your riskiest secrets so you can fix your biggest threats first.
Validate the status of your secrets activity
Secrets risk scoring based on potential impact and exposure
Leverage code context to reduce any false detections
Monitor secrets exposure in private or public repos
{ Remediation }
Prevent Secrets Exposure with
Developer Friendly Workflows
Enable your developers to detect and remove hardcoded secrets directly within their existing tools, enhancing security without disrupting workflow.
Detect and remediate right within the IDE
Streamline remediation workflows through ticketing tool integrations
Auto-resolve remediated secrets
Connect into the CI/CD workflow with Cycode CLI
Detect, block, and monitor secrets in the PR
Frequently Asked Questions About Secret Scanning
What are secrets and why are they important?
Implementing tools and best practices for secrets management, such as secrets detection using a secrets scanner, helps ensure that sensitive information remains secure throughout the development and operational lifecycle.
What is secret detection?
What kind of secrets are found in source code?
Learn more about the top source code leaks and their impact.
Are secrets found only in source code?
Why don’t code reviews find secrets in source code?
Human reviewers may overlook embedded secrets due to their subtle nature, especially in large codebases. Secrets might also be introduced through automated scripts or overlooked configuration files, which are not always subject to thorough manual review.
Automated tools like Cycode are specifically designed to detect secrets are more effective; they systematically scan code for patterns and anomalies indicative of sensitive information.