Proactively Detect and Prevent
Source Code Leakage.
Leverage source code leakage detection that identifies suspicious behavior
and publicly exposed proprietary code before it impacts the business.
{ Prevention }
Prevent Source Code Leak
& Reduce Business Risk
Reduce the likelihood of exposed code, IP, or secrets. Don’t give attackers the opportunity to examine your code base for any exploitable weaknesses.
Proactive auditing of suspicious code access patterns
Auto-detect tool misconfigurations
{ Identification }
Find Your Proprietary Code in Public Repos Before an Attacker Does
Automatically fingerprint proprietary repos and continuously scan both public repos and code-sharing sites for leaked source code.
Continuous public domain scanning
Enhanced detection with intelligent keyword tracking, including user-defined keywords
Automatic secrets scanning in public repos
Auto-resolve source code leakage
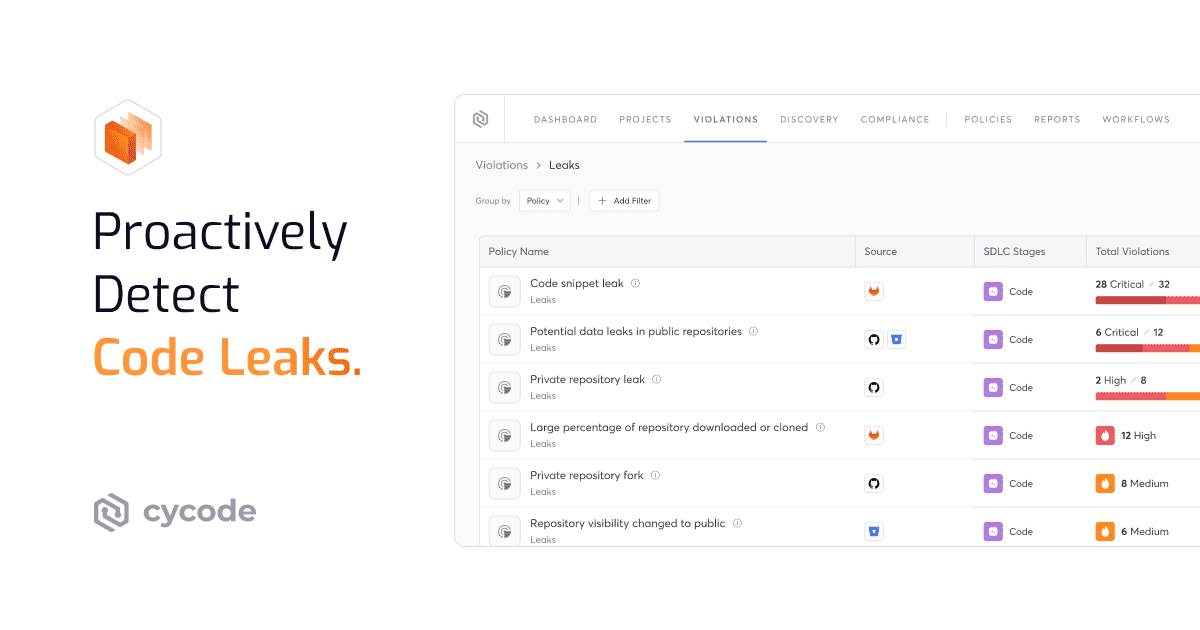
{ Detect }
Detect Any
Anomalous Activity
Identify insider threats by learning how users interact with tools in the SDLC then automatically detect high-risk deviations from learned baselines—like cloning code from unknown locations or cloning excessive repos within a short period of time.
Identify when repos change from private to public
Detect malicious behavior like mass downloading or cloning repos
Analyze source code leakage to surface only real threats
Turn Code Leak Prevention into a
Competitive Advantage
In today's fast-paced, open source environment, protecting your proprietary assets is no longer just a security checklist item; it is a critical business enabler. Effective source code leakage prevention allows your development teams to innovate quickly, knowing that their work and your intellectual property are consistently protected from accidental or malicious exposure, thereby maintaining your market lead and customer trust.
Get a DemoProtect Intellectual Property and Brand Reputation
Advanced source code leakage detection ensures your unique algorithms and product designs stay confidential. This proactive stance minimizes the massive financial and reputational damage from public exposure of assets or security flaws.
Maintain Market Lead: Stop competitors from accessing your core business logic and innovation.
Sustain Customer Trust: Assure partners the systems they rely on are built on secure foundations.
Ensure Data Integrity: Block unauthorized access to systems via exposed credentials or misconfigurations.
Strengthen Compliance and Reduce Breach Costs
A robust leak coding solution is vital for meeting stringent regulatory requirements for data privacy. By proving consistent control over proprietary information, security teams drastically reduce breach risk and mitigate costly non-compliance fines.
Pass Audits Easily: Provide auditable evidence of continuous monitoring and policy enforcement.
Lower Breach Liability: Proactively remediate exposure to directly reduce financial and legal fallout.
Improve Posture Score: Consistently prove sensitive development assets are secured internally and externally.
Empower Developers Without Slowing Delivery
Empower Developers Without Slowing Delivery Integrating security early and automatically transforms it from a blocker into an enabler, checking code right in the developer workflow. This stops a code leak at the commit level, giving developers real-time fixes without forcing context switching.
Maintain Velocity: Eliminate friction with fast, asynchronous checks that don't interrupt CI/CD pipelines.
Shift Responsibility Left: Give developers the power to fix issues themselves before a security review is needed.
Focus on Innovation: Let developers use modern tools confidently, knowing automated guardrails are in place.
Deep Diving Resources
Detect Code Leaks Faster
Frequently Asked Questions
What Is a Source Code Leak?
This exposure can include credentials, keys, and design logic. Once leaked, the code is available to adversaries who can study it for security vulnerabilities or reuse it for competitive advantage. The reality is that source code is hard to protect as it moves across various tools and platforms.
What Are the Most Common Causes of Source Code Leakage?
Furthermore, insider threats, whether malicious or negligent, can intentionally upload proprietary code. Regardless of the intent, these leaks create a critical security incident that requires immediate detection and remediation to prevent further damage. See the top source code leaks for examples.
What Is the Business Impact of a Code Leak?
More critically, it enables attackers to gain unauthorized access to systems by exploiting revealed credentials or known security vulnerabilities. The financial cost of a source code leak includes incident response, regulatory fines, and long-term reputational damage.
How Does Cycode Detect Proprietary Code Leakage Across Public Repositories and Code-Sharing Sites?
This continuous external monitoring is essential because a code leak requires immediate discovery and triage. By effectively detecting source code leakage, Cycode minimizes the time attackers have to exploit your exposed assets.
Can Cycode Prevent Source Code Leaks Before They Occur?
We enforce policies on internal repositories and CI/CD pipelines to prevent secrets and sensitive proprietary information from ever being pushed into any code base, public or private. This proactive code scanning software approach acts as a robust barrier against internal errors that lead to leaks.
How Does Cycode Identify Insider Threats and Anomalous Behavior in the SDLC?
Any deviation from this baseline—such as a developer suddenly cloning an unusually large number of repositories or accessing sensitive code outside their normal working hours, triggers an immediate alert. This behavioral analysis is key to securing your source code against both negligence and malicious insider threats.
Does Cycode Automatically Scan for Secrets, Tokens, and Other Embedded Credentials in Public Repos?
Finding these trade secrets quickly is crucial, as exposed credentials allow immediate, direct compromise of business assets. Cycode's secrets detection capability is a powerful defense against this high-risk form of source code leakage.
What Happens When Cycode Finds Leaked Source Code or Proprietary Assets Online?
We provide the necessary details and evidence to facilitate the immediate revocation of any exposed credentials and begin the process of takedown requests to the hosting platform. This fast response minimizes the window of exposure and limits the damage of the leaked code or detect secrets in source code.
How Does Cycode Reduce False Positives When Flagging Potential Code Leaks?
Furthermore, we use the Risk Intelligence Graph (RIG) to correlate findings. By understanding the context of the leak within the entire SDLC, we ensure that security teams are only chasing verified, high-risk leaks, not wasting time on benign alerts.
Can Cycode Scale Source Code Leak Detection Across Large Complex Organizations With Hundreds of Repos and Developers?
We centralize governance and reporting, allowing security teams to manage all their detection and prevention efforts from a single pane of glass, which is vital for maintaining control under modern development practices and organizational complexity.