We analyzed the first 100 real-world conversations with Cycode Maestro. What we found challenged our assumptions and revealed where practitioners are finding opportunities to save time and gain clarity.
When we launched Cycode Maestro, we had hypotheses about how practitioners would leverage agentic security. They’d analyze for exploitability. They’d generate fixes. They’d ask about violations.
The first 100 conversations tell a much more interesting story.
Across many different enterprise security teams spanning fintech, medtech, and payment industries, the requests that came in weren’t just lookups. They were investigations. Real-time threat checks. Cross-repository audits. Malware detection. Questions that, done manually, would eat up entire workdays or bleed into weekends.
Here’s what we found.
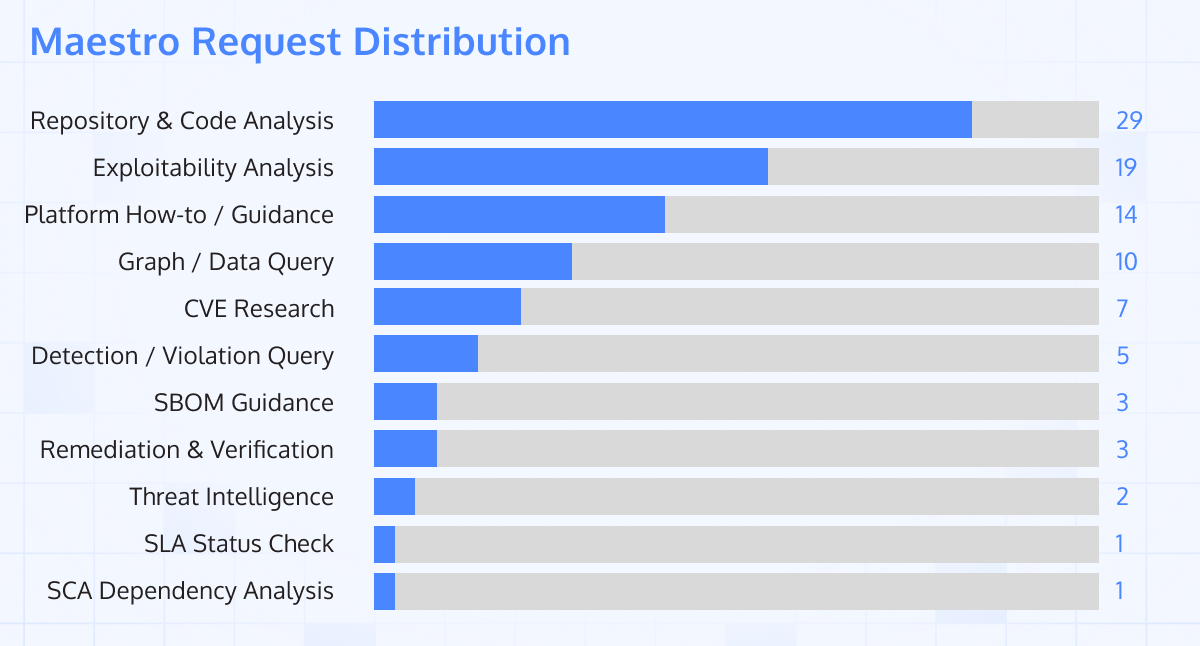
The #1 request category isn’t what we expected
The most common request type was not to fix a violation or analyze exploitability (though this was the second-most common request). Instead, the most frequent conversations were repository and code analysis: “Give me the context of this repo,” “Identify dependencies,” “Run the PR analysis and tell me what’s being imported at runtime.”
This tells us something important. Security teams aren’t just looking for verdicts or actions on open violations. They want to understand the context of code they didn’t write, in repositories they don’t own, across pipelines they didn’t build. They want the kind of knowledge a staff engineer has without having to become one or ask one.
Maestro is doing complex work, not just answering questions
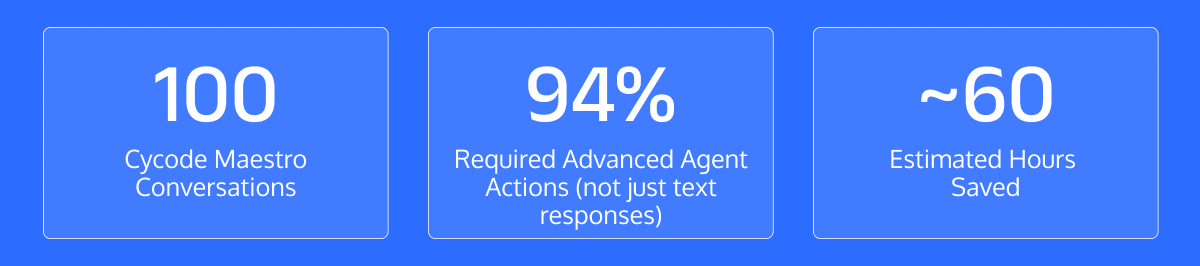
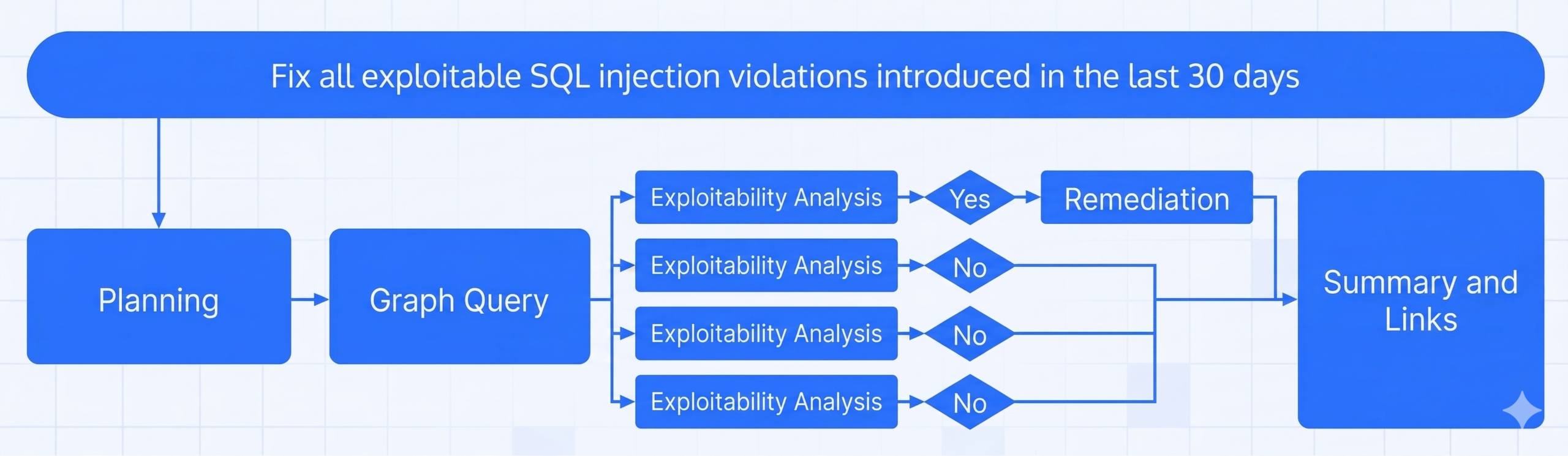
Of the 100 conversations, 94 required Maestro to invoke at least one agent skill beyond a plain text response. The agent queried live detection data, analyzed repository code, ran graph queries across entire organizations, and executed automated remediation, all in response to natural language prompts.
The most complex requests required 3 or more sequential tool calls before producing an answer: planning, querying, analyzing, and synthesizing. These are the interactions where the distinction between “AI chat” and “agentic security” becomes real.
The interactions reveal what’s actually hard
Some of the most compelling conversations weren’t necessarily the most technically complex. Instead, they traversed structural gaps in how security information is discovered, communicated, and acted on. By doing so, they answer complex questions that typically take hours to investigate.
Here are some of the most interesting conversations:
Threat intelligence: A news article became a security query in real time
A practitioner pasted a link to a news article about the recent Trivy supply chain attack and asked: “Do I have any exposure to this?” Maestro queried the organization’s entire codebase across all repositories and returned a verdict in seconds. The same check done manually involves opening every dependency file across all projects.
Scale analysis: 41 open violations triaged in one conversation
Instead of reviewing each SCA violation individually, one user asked Maestro to assess exploitability across all findings in a repository. Maestro surfaced the two critical issues, assessed risk across the remaining 39, and explained why most weren’t exploitable in the current environment. The output of a full triage session, delivered conversationally in moments.
Malware detection: Dangerous npm install hooks identified before deployment
A user asked Maestro to analyze install scripts in a repository flagged for review. Maestro identified three npm lifecycle hooks (preinstall, postinstall, and prepare) containing commands to exfiltrate environment variables to a remote endpoint. It surfaced the exact script contents, explained the attack vector, and flagged the severity before the code reached production.
The time savings are already significant
We estimated the time saved by mapping each substantive request to benchmark estimates for the equivalent manual task. The results are conservative (they exclude follow-up messages and assume the low end of time ranges for complex work).
Across the first 100 conversations (94 of which required substantive tasks), Cycode Maestro saved an estimated 60 hours.
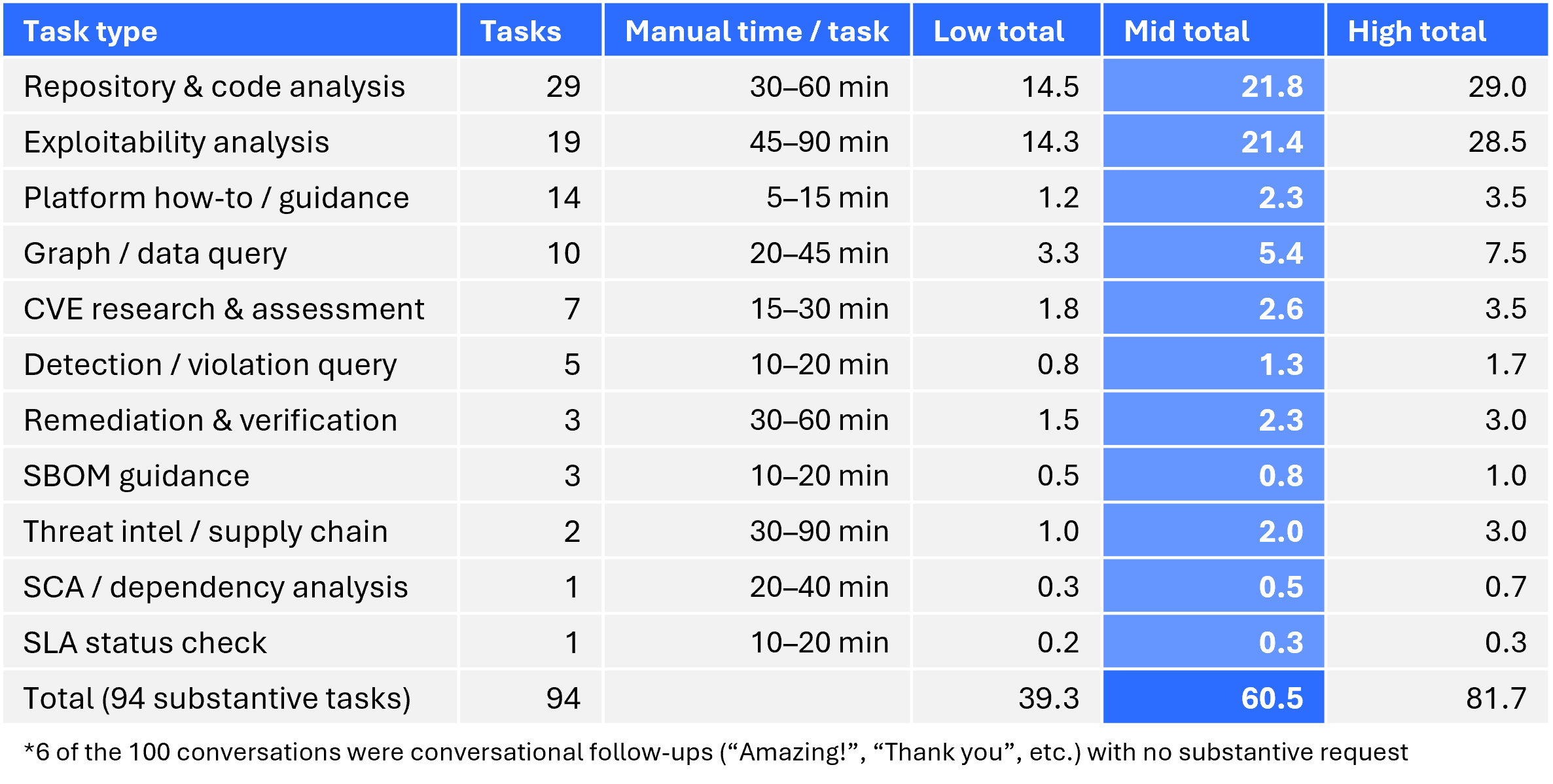
Notably, the tasks with the highest time delta between manual and AI-assisted are exactly the tasks Maestro was asked to do most often: cross-repository searches, exploitability assessments, and code context analysis. This isn’t a coincidence. Practitioners offload their most time-consuming work if there is an alternative solution that can handle it.
What this tells us about the adoption of AI for security
A few patterns stand out from this dataset that are worth noting.
Practitioners turn to AI agents for their highest-friction tasks first. The requests that dominated weren’t the easy ones. They were the ones that required the most cognitive overhead, the most context-switching, or the most time sifting through information. Security teams aren’t using Maestro as a search engine. They’re using it as a force multiplier for the manual tasks that keep them from other important work.
Natural language queries unlock data and insights faster. Multiple users asked questions that could theoretically be answered through Cycode’s interface. However, they chose to use natural language to arrive at the answer. Expressing the query in natural language is fundamentally different from navigating filter dropdowns. “Which of my repos uses this library?” is a natural question. Selecting the right combination of filters is not. Both have their places and benefits, and now users have more choices in how they want to engage with their data.
AI agents reduce time to clarity, not just mean time to triage and remediate. The most valuable interactions were the ones that gave practitioners a clear answer they could act on, whether that was “not exploitable, here’s why” or “you still have exposure, here’s what to check.” Clarity is the scarce resource in security workflows, and it’s what these conversations delivered.
Finally, we’re early. 100 conversations is an early glimpse, not a significant dataset. But the patterns are emerging and consistent enough to be meaningful, and they’re already shaping how we think about where we take Maestro next.
See Maestro in action today. Get a demo.


