Automotive Software Security for Modern Development
The race toward software-defined vehicles has turned the garage into a data center. As automotive software complexity explodes through sprawling supplier ecosystems and regulatory pressure, Cycode provides the AI-native foundation needed to secure the entire automotive software development lifecycle without stalling innovation.
{the gaps}
Human-LedAutomotive Software Security Is Broken
The move toward software defined vehicles didn't just accelerate development; it fundamentally broke traditional automotive security models where human-led engineering teams alone can’t keep up.
Get a DemoEveryone's a 10x Developer. Your Compliance Team Isn't.
Everyone's a 10x Developer. Your Safety Team Isn't. AI has supercharged development velocity for vehicle software and mobility services. But when safety-critical security can’t keep pace, risk scales as fast as the code itself. Moving at 1x speed to secure 10x AI-generated code creates a safety gap that traditional gatekeeping cannot close.
Financial Attacker Velocity Has Skyrocketed by 10x
Vehicle Attacker Velocity Has Skyrocketed by 10x Safety systems and telematics are being targeted faster than ever. AI is amplifying automotive attackers, enabling simultaneous targeting across traditional embedded systems and new cloud-native attack surfaces. 10x attackers use automation to find entry points into the vehicle's bus or backend before manual security checks are even triggered.
AI Writes the Banking Code and Expands the Attack Surface
AI Writes the Vehicle Code and Expands the Attack Surface AI-native components and MCP servers are now part of your vehicle's infrastructure. Also, AI is authoring pull requests, reviewing commits, and automating tests for software defined vehicles, amplifying risk across both infrastructure and code generation. This expanded attack surface requires a Context Intelligence Graph to track how AI-generated code affects the physical safety of the driver.
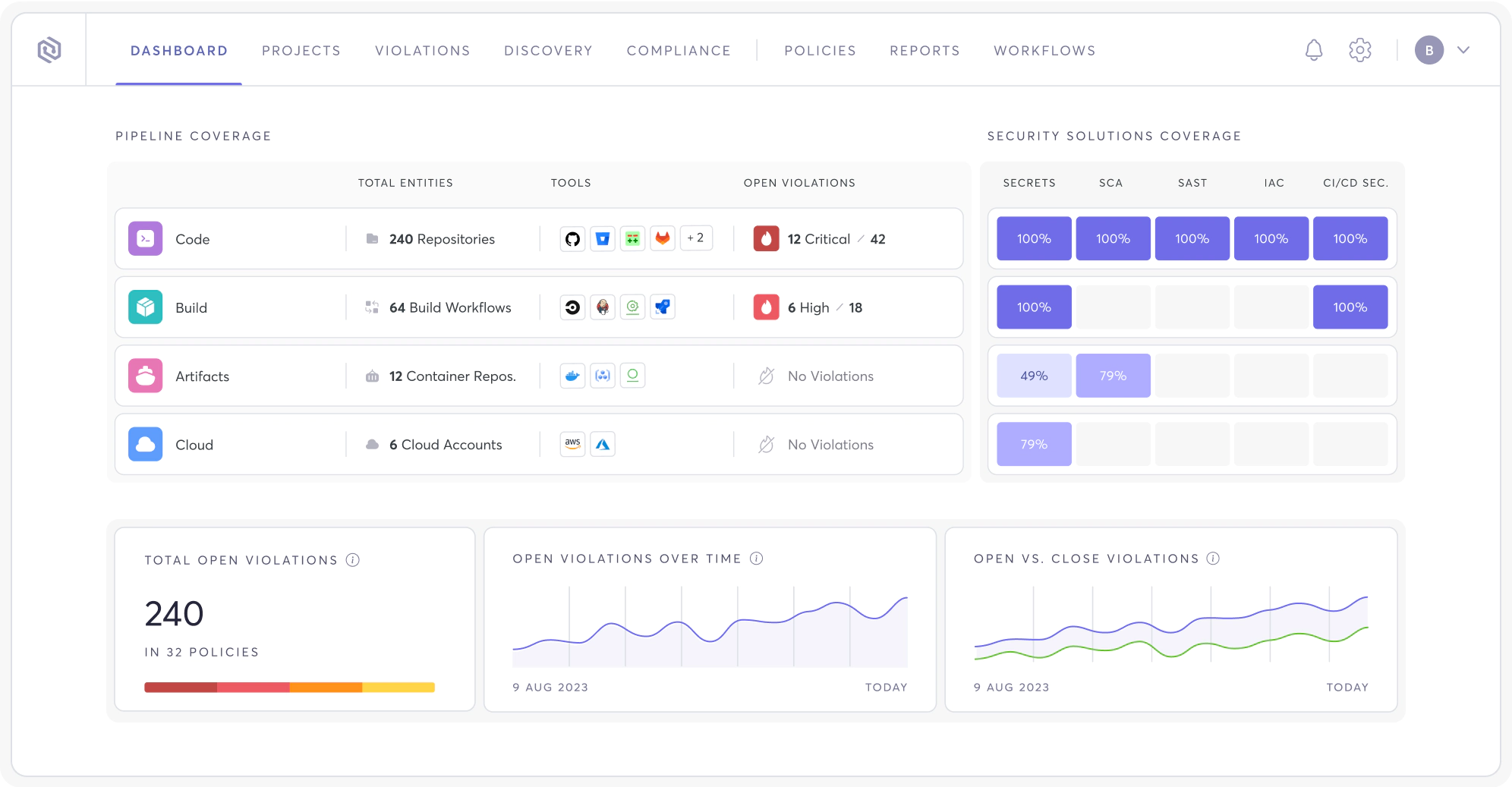
{Development Coverage}
Automotive Software Development Security
Across the SDLC
Automotive organizations now rely on a mix of open source security protocols, complex CI/CD pipelines, and cloud infrastructure to deliver mobility services and vehicle software. Securing this environment requires a unified view that connects code, pipeline, and cloud context in real time.
Unified Visibility Gain a single source of truth across proprietary code, third-party libraries, and supplier-provided binaries.
Agentic Triage Use AI agents to prioritize vulnerabilities that actually impact vehicle safety and data privacy.
Proactive Guardrails Prevent secrets and misconfigurations from ever leaving the developer's workstation.
{Software Supply Chain}
Manage Open Source and Third-Party Code Risk
Securing the software supply chain is critical as software development for automotive increasingly relies on open source components and black-box supplier deliveries.
Real-Time AIBOM & SBOM: Maintain a living inventory of every model and library used in your vehicle's stack.
Supplier Governance:Automatically scan incoming supplier code for backdoors, secrets, and high-risk vulnerabilities.
Reachability Analysis:Determine if a CVE in an open source library can actually be triggered by your vehicle's runtime environment.
{Secure Development Workflows}
Strengthen Automotive CI/CD
and DevSecOps Pipelines
Protecting the integrity of the automotive software development process means securing the tools and repositories that engineering teams use to build and deploy.
Hardened Pipelines: Detect and block malicious tampering within your CI/CD runners and build environments.
Secure Development Workflows:Seamlessly integrate security checks into the DevSecOps workflow to empower developers to fix code as they write it.
Code Integrity:Ensure that the firmware version running on the vehicle is exactly what was signed and verified in the build stage.
{Backend and API Security}
Secure Automotive Cloud
and Telematics Development
Connected vehicle platforms depend on massive cloud backends. Securing these APIs is essential to prevent unauthorized remote access to vehicle functions.
API Discovery: Automatically map every endpoint used in telematics and mobility services to identify "Shadow APIs."
Data Flow Protection: Monitor how sensitive vehicle and driver data moves through your secure cloud-based automotive software.
Infrastructure as Code (IaC): Identify cloud misconfigurations that could expose your backend infrastructure to the public internet.
{Policy and Governance}
Enforce Automotive Security Policies at Scale
Maintaining SDLC governance across distributed global engineering teams and hundreds of suppliers requires automated policy enforcement.
Compliance-as-Code:Automatically enforce security policies aligned with global automotive standards.
Custom Security Logic: Use Maestro to orchestrate complex security workflows that match your unique engineering requirements.
Continuous Monitoring: Shift from periodic audits to a state of constant compliance readiness.
Maintain Secure Cloud-Based Automotive Software at Scale
The transition to software-defined vehicles requires a unified application security platform that provides visibility across distributed teams and global suppliers. Cycode consolidates risk intelligence to ensure that every update pushed to a vehicle is as secure as it is functional.
Centralized Automotive Software Risk Management
Gain a bird's-eye view of software risk across all repositories and pipelines. This allows security leads to mitigate risks based on actual safety impact rather than just alert volume.
Support Automotive Cybersecurity Standards
Align your automotive software development with ISO/SAE 21434 and UNECE WP.29 lifecycle requirements through automated evidence collection and real-time posture reporting.
Reduce Fragmentation Across Automotive Development
Consolidate fragmented app security tools into a single AI-native platform. This reduces the operational burden on your security team while accelerating developer velocity.
Frequently Asked Questions About Application Security Testing (AST)
What Is Automotive Software?
Because these systems are deeply interconnected, a single security risk in a third-party library or an exposed API can have direct physical implications. Securing this software requires a code-to-cloud approach that accounts for both the code running in the vehicle and the backend services that support it.
Why Is Secure Automotive Software Development Becoming Critical?
The shift toward software-defined mobility means that a breach isn't just a data leak; it's a safety hazard. Implementing agentic security allows manufacturers to identify and fix vulnerabilities before they can be exploited in a production environment.
How Does Open Source Risk Impact Software Development for Automotive?
Managing open source security is no longer optional for OEMs. By using the Context Intelligence Graph, teams can see not just which libraries are vulnerable, but which ones are actually reachable and exploitable within the vehicle's unique architecture.
How Do Automotive OEMs and Suppliers Manage Software Supply Chain Security?
This collaborative security model ensures that suppliers meet the same rigorous standards as the OEM. By automating the verification of supplier code and binaries, manufacturers can reduce the risk of backdoor entries and dependency confusion attacks.
What Is ISO/SAE 21434 and How Does It Impact the Automotive Software Development Process
This standard forces a move away from point-in-time testing toward continuous monitoring. Cycode supports this by automating the evidence-gathering process, making it easy to prove that every software update has undergone rigorous security validation.
What Is UNECE WP.29 and What Does It Require from Manufacturers?
Cycode helps manufacturers meet these requirements by providing an automated audit trail for every software change. This ensures that every "over-the-air" (OTA) update is documented, verified, and safe for the end user.
How Does DevSecOps Apply to Software Development in the Automotive Industry?
By shifting security left, developers can identify flaws as they write code. This prevents the costly "re-work" that happens when a critical vulnerability is discovered only after the software has been integrated into the vehicle hardware.
How Can Automotive Organizations Monitor Software Risk Across the SDLC?
This connective intelligence provides a clear view of the "risk path." It allows security leaders to see exactly which code changes, developers, and build pipelines contributed to a specific production risk.
What Role Does Application Security Play in Software-Defined Vehicles?
Without a strong security platform, these systems remain vulnerable to unauthorized access. Cycode ensures that the software powering these features is free from secrets, vulnerabilities, and malicious tampering.
How Does Cycode Support Automotive Software Development Security?
Our platform replaces fragmented tools with a single, agentic defense system. This allows automotive engineering teams to focus on building the future of mobility without worrying about the hidden risks in their software supply chain.