The National Institute of Standards and Technology (NIST) first released its Cybersecurity Framework in 2014 in response to an Executive Order mandating improved cybersecurity for critical infrastructure.
The goals of this NIST framework include hardening cybersecurity among government entities and institutions, however, this framework is also intended to be adopted by businesses of all sizes. The following overview is designed to serve as an introduction to the NIST best practices and standards.
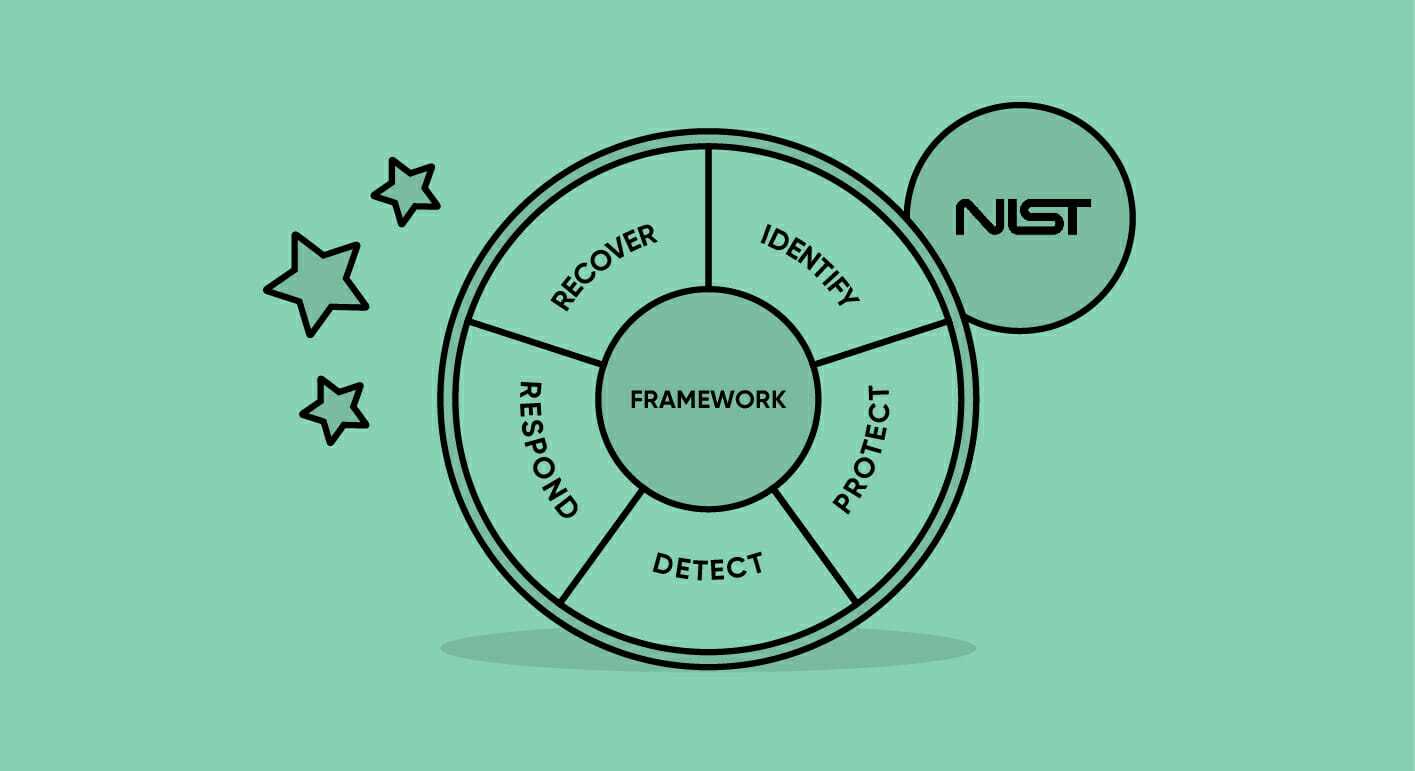
The NIST Cybersecurity Framework (NIST CSF) consists of three main parts: the Framework Core, the Implementation Tiers, and the Framework Profiles. The Framework Core exists as specific guidelines for organizations to adhere to, the Framework Tiers provide a measuring stick for organizations to characterize their approach to cybersecurity, and Framework Profiles help an organization describe its current security posture and identify its organizational cybersecurity goals.
NIST Cybersecurity Framework Core
The Framework Core is a set of cybersecurity activities, outcomes, and informative references that are common across sectors and critical infrastructure. The components of this core help individual organizations develop current and target profiles by providing detailed guidance for each.
Identify
The identify section of the core is aimed to develop the organization’s understanding of cybersecurity risk within its systems, assets, data, and capabilities.
| Asset Management | Assets are identified and managed consistent with their relative importance to the organization’s risk strategy. |
| Business Environment | The organization’s mission, objectives, stakeholders, and activities are used to inform cybersecurity decisions. |
| Governance | The policies to manage the organization’s requirements are understood and inform the management of cybersecurity risk. |
| Risk Assessment | The organization understands the cybersecurity risk to organizational operations, organizational assets, and individuals. |
| Risk Management Strategy | The organization’s priorities are used to support operational risk decisions. |
| Supply Chain Risk Management | The organization’s priorities are established and used for decisions associated with managing supply chain risk. |
Protect
Protecting the components identified as factors introducing cybersecurity risk is a key function of the NIST Cybersecurity Framework (NIST CSF) core. This entails developing and implementing the appropriate safeguards to ensure the delivery of critical infrastructure services.
| Identity Management and Access Control | Access to assets is limited to authorized users and is managed consistently. |
| Awareness and Training | The organization’s personnel and partners are trained to perform their cybersecurity duties. |
| Data Security | Information and records are managed to ensure confidentiality, integrity, and availability of information. |
| Information Protection Processes and Procedures | Security policies are maintained and used to manage information systems and assets. |
| Maintenance | Maintenance and repairs are performed consistent with policies and procedures. |
| Protective Technology | Technical security solutions are consistently managed to ensure the security of systems and assets. |
Detect
The first step to mitigating a cybersecurity attack is to detect the event in the first place. Detect functionality allows for timely discovery and identification of cybersecurity events and may be achieved by methods including custom alert policies.
| Anomalies and Events | Anomalous activity is detected and the potential impact of events is understood. |
| Security Continuous Monitoring | The information system and assets are monitored to identify cybersecurity events and verify the effectiveness of protective measures. |
| Detection Processes | Detection processes and procedures are maintained and tested to ensure awareness of anomalous events. |
Respond
Developing and implementing an appropriate course of action specific to a detected cybersecurity incident fits within the category of responding within the NIST CSF. This further entails creating procedures designed to contain the blast radius of a cybersecurity incident in an effort to contain the impact.
| Response Planning | Response processes and procedures are in place to ensure proper response to detected cybersecurity incidents. |
| Communication | Response activities are coordinated with internal and external stakeholders. |
| Analysis | An analysis is conducted to ensure optimal response and support recovery activities. |
| Mitigation | Activities are performed to prevent the expansion of an event, mitigate its effects, and resolve it. |
| Improvements | Organizational response activities are improved by incorporating lessons learned from current and previous mitigation activities. |
Recover
Designing a resilient system that can bounce back after a cybersecurity incident is the key to the recovery function of the NIST Cybersecurity Framework. Well-designed recovery procedures support a timely return to normal operations as well as contingency plans to reduce the impact of a cybersecurity incident.
| Recovery Planning | Recovery processes and procedures are executed and maintained to ensure the restoration of systems or assets affected by cybersecurity incidents. |
| Improvements | Recovery planning and processes are improved by incorporating lessons learned into future activities. |
| Communication | Restoration activities are coordinated with internal and external parties. |
NIST Cybersecurity Framework Implementation Tiers
The Framework Implementation Tiers are designed to provide context on how an organization views cybersecurity risk and the contingency strategies in place to mitigate this risk. Unlike Google’s SLSA where higher levels represent greater maturity, higher Tiers within the NIST CSF represent increasing degrees of rigor and sophistication in cybersecurity risk management practices. The desired Tier for an organization should be selected based on the organization’s goals, the ease of implementation, legal requirements, and the risk level that is acceptable to the organization; Progression to higher Tiers is encouraged when a cost-benefit analysis indicates feasible reduction to cybersecurity risk.
Tier 1: Partial
Organizations adhering to Tier 1 usually manage risk in an ad hoc manner without formalized risk management practices. This limited awareness of cybersecurity risk at the organizational level results in risk being managed reactively or on a case-by-case basis. In addition, the organization does not understand its role within the software supply chain and does not collaborate with other organizations to improve the state of cybersecurity–ultimately, the organization is unaware of the supply chain risks associated with the products that it provides or uses.
Being identified as Tier 1 implies the organization should become risk-informed to move their standing into Tier 2. While rigorous cybersecurity policies are not required for every organization, a business should have some baseline awareness of its cybersecurity standing.
Tier 2: Risk-Informed
Organizations are aware of cybersecurity risks, have mitigation strategies to utilize in the case of a breach, and have the needed resources allocated to promote cybersecurity measures. The implementation of cybersecurity measures does not need to be complete, but cybersecurity prioritization should be well informed by risk assessments, the threat environment, and the business’s objectives. The organization also understands aspects of its role within the software supply chain.
Tier 3: Repeatable
The NIST Cybersecurity Framework repeatability tier means that an organization has implemented cybersecurity standards company-wide and is able to consistently respond to cyber-attacks and breaches. Employees are informed of risks and are trained to apply policy consistently.
Tier 4: Adaptive
Representing total adoption of the NIST Cybersecurity Framework, the adaptive tier indicates that an organization is prepared to proactively detect threats and predict issues based on current trends and the existing IT architecture. The organization also understands its dependencies and dependents in the larger ecosystem.
NIST Cybersecurity Framework Profiles
The Framework Profile describes the alignment of the framework core with the organization’s requirements, risk tolerance, and resources. This allows for a roadmap towards reducing cybersecurity risk to be established that reflects business goals and reflects legal requirements, industry best practices, and risk management priorities. Framework Profiles may be described in two main states: current profile and target profile.
The current profile of an organization indicates the cybersecurity outcomes which are currently being achieved. This describes the current standing of an organization from a risk management standpoint. Reassessment should occur periodically as changes and improvements are implemented to verify that cybersecurity requirements are still being met. It is important to note when outcomes are partially achieved as this helps support subsequent steps in the effort to match the current profile to the target profile.
The target profile is an indication of the outcomes needed to achieve the desired cybersecurity risk management goals. Comparing the current profile to the target profile may reveal gaps to be addressed to meet cybersecurity risk management objectives. As mentioned, organizations may monitor progress in achieving these goals through iterative updates to the current profile. These goals outlined within the target profile should be incorporated when planning out additional components and adding dependencies to projects within the organization; these may also serve as a checklist to help verify that all cybersecurity features are implemented. A target profile can serve as a powerful communication tool to convey cybersecurity risk management requirements to an external service provider.
Implementation Goals
The implementation plan is characterized as a whole-of-nation approach to cybersecurity but also includes international pushes. Though only the federal government’s organizations are to be held to the cybersecurity standards outlined here, private sector organizations have the option to utilize the NIST Cybersecurity Framework. This framework is designed to be used for self-assessment and has five key goals:
- Examine the cybersecurity of an organization and determine the target implementation tiers
- Determine the current implementation tiers as a means of evaluating the organization’s current approach to cybersecurity.
- Develop outcome goals and target profiles
- Create a roadmap towards the desired outcome goals
- Calculate the degree of controls, catalogs, and technical guidance implementations based on the Cyber Security Framework
Conclusion
Private companies including Apple, Google, Amazon, Microsoft, IBM have each announced their own pushes to improve cybersecurity within their domains. Some, such as Google’s SLSA, have already established a baseline level of support and will continue to increase in maturity. Regardless of the approach chosen, having the right tools available to help is paramount.
Latest Guidance: The NIST SSDF
In light of recent cyberattacks, including the attack on Colonial Pipeline which triggered a gas shortage in the southeast, the Whitehouse unveiled an Executive Order that provides additional guidance on improving the state of cybersecurity. NIST and the Cybersecurity and Infrastructure Security Agency (CISA) have aligned themselves with the goals of this Executive Order and have set out to collaboratively build a cybersecurity framework for critical infrastructure stewards to adhere to.
The Whitehouse’s Executive Order issued on May 12, 2021, charges multiple agencies, including NIST, with enhancing cybersecurity through a variety of initiatives related to the security and integrity of the software supply chain. In response to the EO titled “Improving the Nation’s Cybersecurity (14028),” NIST created the Secure Software Development Framework (SSDF) to help improve federal agencies’ cybersecurity. This framework takes the recommendations of the NIST CSF and applies these lessons, plus guidance from agencies including OWASP, towards the software supply chain to improve security.
How Cycode Can Help
Requirements of the NIST Cybersecurity Framework can be supported through the use of tools such as the Cycode platform. Cycode can help improve the security of your software supply chain by providing complete visibility into enterprise DevOps tools and infrastructure. Cycode’s Infrastructure as Code capabilities include comprehensive security scanning and preventing escaped secrets, environmental drift, code leaks, and other common issues, all within flexible developer-friendly workflows. Once integrated into developer workflows, each commit and PR is scanned for issues including hard-coded secrets or potential misconfiguration, and alerts are issued appropriately. Remediation is available both through a GUI and within the PR.
Cycode helps establish strong governance over every point of the SDLC by providing a cross-SCM inventory of all users, contributors, teams, organizations, and repositories in your organization; this governance extends into providing more oversight into changes made to code as a means of further protecting key code. Required functionality of the NIST Cybersecurity Framework such as cybersecurity event and anomaly detection is made significantly easier through use of tools such as Cycode’s custom policy builder. Cycode also helps you automatically audit access privileges to identify and reduce excessive, unused privileges, and implement separation of duties. Furthermore, Cycode helps ensure that strong authentication and secure development practices are in place. This helps apply security best practices for IaC code when using Terraform, Kubernetes, YAML, ARM, and CloudFormation.
Want To Learn More?
A great place to start is with a free assessment of the security of your DevOps pipeline.