Application Security
for the AI Revolution
Purpose built for the 10X developer output. Combining the best of AST, ASPM, and SSCS with the only modern "always-on" platform to stop software risk, not developer velocity.
Application Security is in
a State of Chaos
Every developer’s now a 10X developer in this new AI era, and traditional Application Security can’t keep up. Siloed tools are creating inefficiencies, alert fatigue, and misalignment between security and dev teams — slowing velocity and innovation.
Your New Application Security
Operating Model to Fix What Matters
Application Security Testing (AST)
Find and fix vulnerabilities in your code with advanced SAST, SCA, IaC, and container scanning tools.
Software Supply Chain Security
Secure your CI/CD pipelines by detecting hidden secrets, fixing misconfigurations, and preventing code leaks.
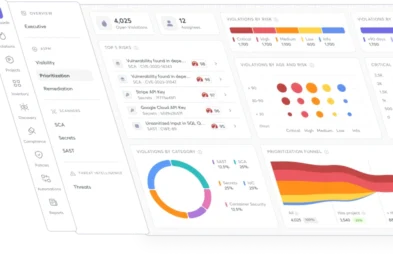
ASPM
Achieve complete visibility into your application security posture with risk prioritization and actionable remediation.
Cycode's AI-Native Application Security Platform
is the New Enterprise Standard
Insights
Root Cause Analysis
DevEx
Analytics
Governance
Complete Visibility and Control over Software Risk
Gain full visibility into application risk at every layer, unifying insights across all your tools, and uncover shadow SDLC technologies.
One Unified View of AppRisk
Eliminate silos, integrate 100+ tools, and instantly switch on risk detection for a full picture into your security posture.
Enterprise-Grade Proprietary Scanners
Comprehensive, and modern scanning across Secrets & NHIs, SAST, SCA, Container, IaC, CI/CD Pipeline, Code Leaks, and more.
Full Visibility of the Software Factory
Achieve continuous visibility with SDLC technology inventory of your code dependencies, artifacts, APIs, and SaaS services.
Prioritize Critical Risks, Maximize Productivity, Maintain Trust
Deliver high-fidelity contextual results, focus on critical business risks, reduce developer friction, and eliminate wasted time on irrelevant issues.
Focus Only On What Matters Most
Intelligent risk scoring engine based on CVSS, CISA KEV, EPSS, business impact, runtime intelligence, and other key impact factors.
Intelligent Code to Runtime Context
Unlock the power of code to runtime context designed to help identify what matters.
Uncover and Analyze Your Exposure Path
Leverage rich context to visualize your risk exposure path and prioritize based on business impact.
Streamlined Remediation with Faster Results
Reduce MTTR and developer friction with precise, context-driven fixes and automated no-code remediation workflows.
Actionable Context & Code Ownership Mapping
Know who needs to fix it, where to fix it, and how to fix it.
Security That Works the Way Your Devs Do
Empower developers with integrated security across their IDE, PR, or CI/CD to prevent and fix risks faster.
AI-Driven Code Fixes & No-Code Remediation
Accelerate secure development and resolve issues instantly with contextual AI fixes and no-code automation.
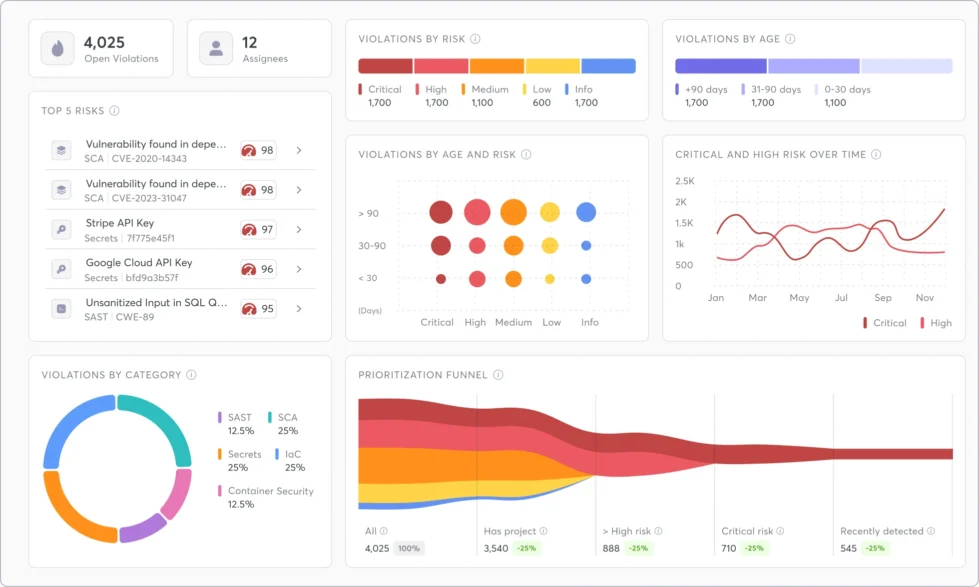
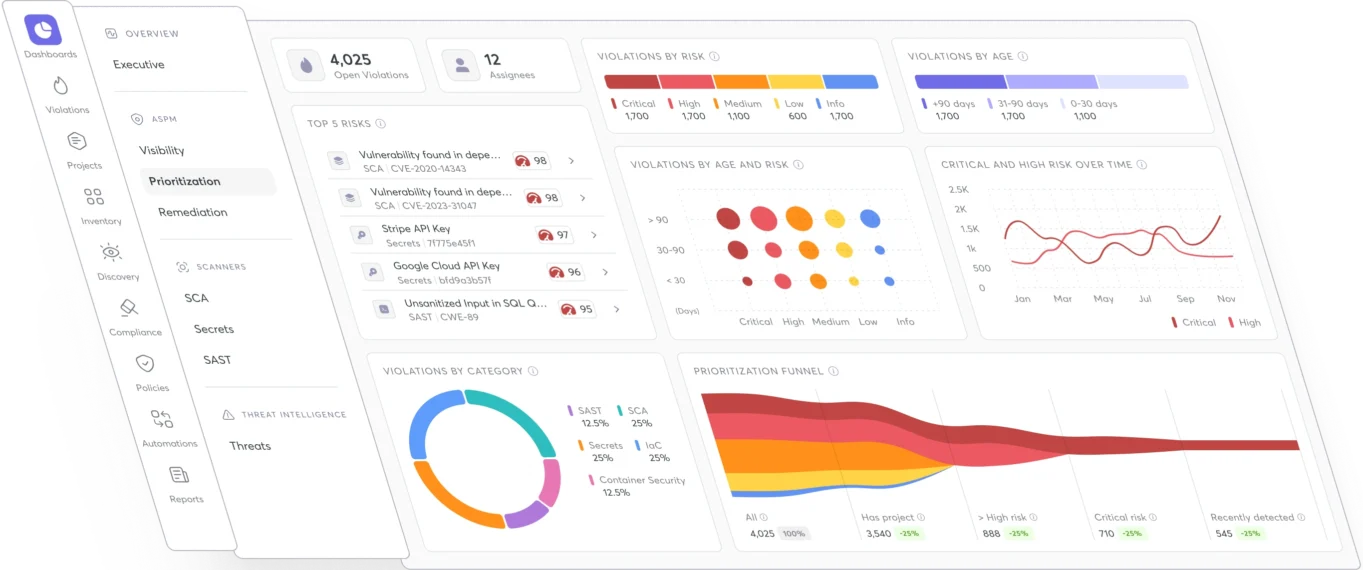
Visualize Security Insights, Track Progress, & Drive Action
Gain complete visibility into your Application Security posture with real-time analytics and customized dashboards.
Centralize Your Security Data
Aggregate and analyze insights from all of Cycode’s Enterprise Grade scanners and third party tools into one unified dashboard.
Customize Your View, Measure What Matters
Build tailored reports and dashboards, from SBOM generation to your developer’s engagement metrics.
Empower Your Teams with Actionable Insights
Drive informed decisions with visual analytics that track progress like MTTR and SLA’s to highlight areas of risk.
Automate Compliance, Streamline Audits, & Ensure Evidence
Reduce any manual effort, simplify audits, and maintain continuous compliance with automated evidence collection.
Audit Once, Comply with Many
Align with multiple standards like SSDF, ISO, SOC2, CIS Benchmarks, DORA, PCI, and many more.
Prove Compliance with Confidence
Ensure your Application Security program meets regulatory and industry standards with verifiable evidence.
Customize and Simplify Compliance
Eliminate manual efforts by streamlining attestation and compliance workflows.
Here, Take the Application Security Magic Wand
Risk Intelligence Graph (RIG)
Find Answers Across Your SDLC. Gain actionable SDLC insights with automated risk detection, seamless remediation, and intuitive natural language queries.
Change Impact Analysis (CIA)
Keep Tabs On Risky Material Changes. Spot material changes early, prioritize risks, and streamline remediation to reduce manual effort and developer friction.
Cycode AI
Instant Context, Faster Fixes. Cycode AI supercharges your security and development teams, empowering them to remediate risks and secure your organization with 10X the speed and precision.
Code Context Analysis (CCA)
Visualize, Map, and Analyze Your Entire SDLC. Uncover, map, and analyze every component in your application code so you can connect the dots across your organization's environment.
Developer Experience
Security That’s Easy for Developers. Deliver context-rich, low friction fixes directly into your developer workflows with no context switching or bottlenecks.
Compliance
Automated Evidence, Instant Assurance. Align & attest with SSDF, SOC2, and ISO standards with always-on compliance and no manual overhead.
Plug in Your Stack.
Control It All.
Plug in Your Stack.
Control It All.
Cycode connects to your existing tools and infrastructure
for full coverage and control—without disrupting workflows.
Don’t Listen To Us, Hear it From Our Customers
"Cycode has helped us with visibility and surfacing the security risk that exists in our software development process.”
"I really like the amount of solutions and third party integrations Cycode supports so I can populate all results into a single place."
"With Cycode Al's Auto Fix and Remediation, our developers resolve vulnerabilities in record time, boosting productivity and code quality.”
Get StartedGet a Personal Demo
See how Cycode combines the best of AST, SSC and ASPM with the only modern “always on” platform to stop software risk not developer velocity.